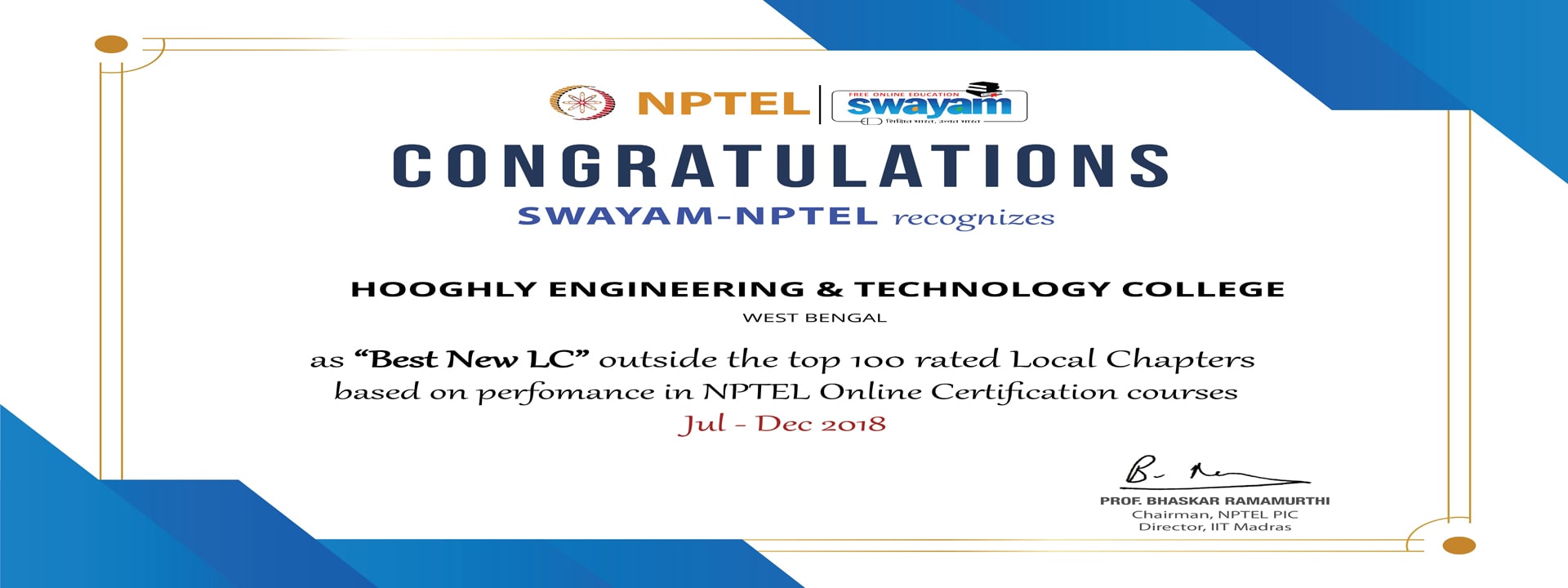
- About Us
- Admission Details 2024
- Courses Offered
- IQAC
- About IQAC
- Composotion
- Meetings
- Reports
- NAAC SSR
- Criterion1-Curricular Aspects
- Criteria-2 Teaching Learning and Evaluation
- Criteria 3-Research,Innovations and Extension
- Criterion 4-Infrastructure and Learning Resources
- Criterion 5-Student Support and Progression
- Criterion 6-Governance,Leadship and Management
- Criterion 7-Institutional Values and Social Responsibilities
- Faculty
- Student Facilities
- Training & Placement
- Tenders
- Gallery
- Campus Life